A new malicious campaign is using more than 200 typosquatting domains to masquerade as popular apps and brands. The new Android virus makes you believe that you are in a legit webpage in order to steal your money or attack your phone.
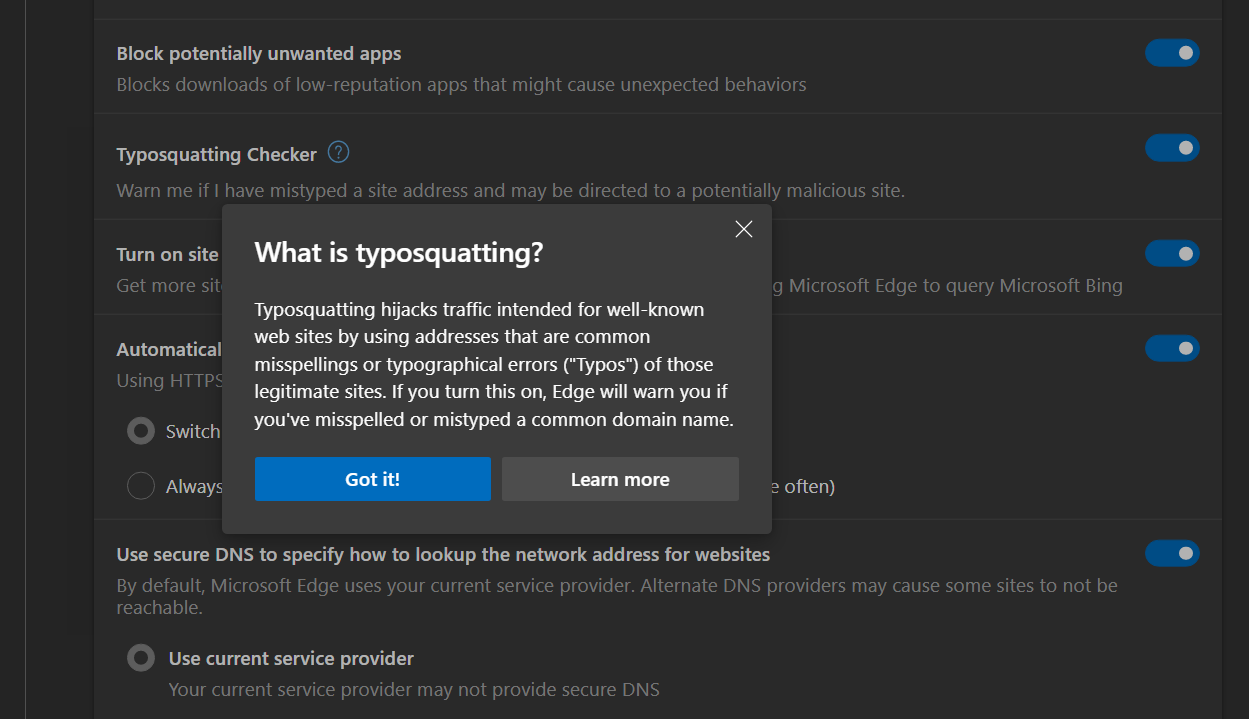
A typosquatting domain is registered to favor deception. The name of the domain is pretty similar to the original one, but you enter by mistake and the visual elements are similar. The most common type of malicious typosquatting webs change one or two letters to deceive users.
The technique is not new in viruses and digital threats. The hackers know that typos are very common and take advantage of that. The new Android virus also works in Windows operative system. The malicious websites are clones of popular ones or the modifications are almost imperceptible.
The trap for users
In order to catch the user, the hackers expect you to make a typo when entering the URL. There are also the e-mail and phishing SMS alternatives, as well as direct messages or links in social networks. The objective of these traps is to lure more unaware users.
There are several domains that simulate being online stores such as Google Play, APKPure or APKCombo. There is also a variety of service apps such as PayPal, Snapchat, TikTok or Google Wallet that are used to introduce Android virus in your device. In total, 27 brands have been identified until now. The masquerade apps make the user download malicious files on Android and Windows alike.
The false Play Store example
A false website imitates Google Play Store and makes you download a Google Wallet APK. The real APK you download is called ERMAC, a bank trojan that attacks bank accounts and crypto wallets. The malware can steal confidential data, SMS, contacts and a list of your installed apps. It also steals your credentials through phishing webs in the home screen of the victim.
Some of the detected domains include:
- payce-google[.]com: it masquerades as Google Wallet
- snanpckat-apk[.]com – it masquerades as Snapchat
- vidmates-app[.]com – it masquerades as VidMate
- paltpal-apk[.]com: it masquerades as PayPal
- m-apkpures[.]com – it masquerades as APKPure
- tlktok-apk[.]link: it masquerades as TikTok download portal
The Cyble report focus on Android malware but the campaign is wider and it also has effect on Windows system. It can masquerade as several mobile apps and services, as well as crypto websites and tools. There are also reports on Tor web browser, Ethermine, MetaMask and Figma impostors. There are at least 200 domains that fell victim to this method.
Be careful on the web
The best advice is not to enter any website domain from a message in your phone. The most secure way is to write the URL on your own. If you are going to install an app, try using the Google Play Store not an APK file. If you have even a little suspicion you should not download the file. You can also use an antivirus in order to check for malware infection.
